Cyber adversaries are tenacious – they employ any possible means and all the tools at their disposal to locate and exploit weaknesses in their targets’ defenses. Potential attack surfaces continue to multiply and diversify as a consequence of expansion across hybrid IT (cloud, edge, and on-premises), Internet of Things, and emerging wireless technologies. More than ever, businesses need effective security services, ensuring protection against multiple attack vectors. Unfortunately, many organizations do not have enough dedicated security resources to maintain this level of protection.
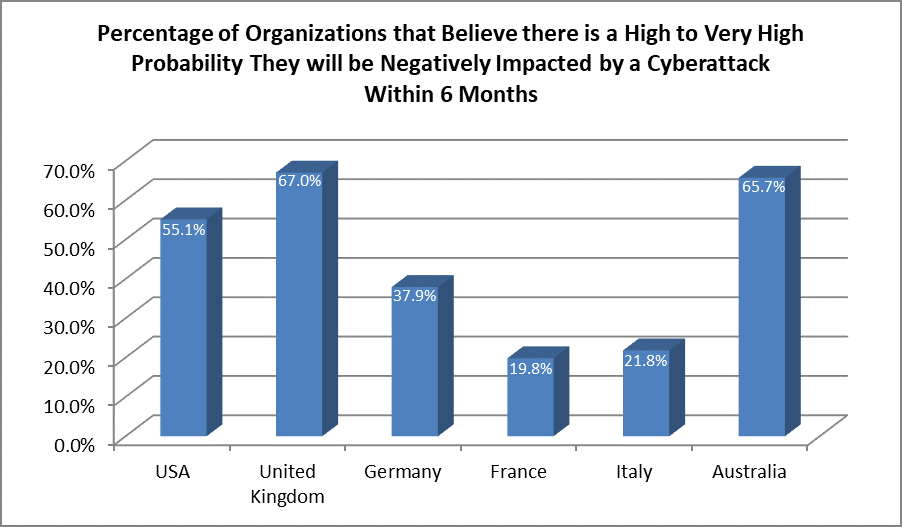
Vulnerabilities can be defined as errors or weakness within software or IT systems that enable an unauthorized user to access sensitive data, gain control, or deny access to authorized users. Nearly all devices and systems will have some vulnerability in their code. According to a recent Frost & Sullivan survey, 40% of midsized organizations consider system vulnerabilities as their main cybersecurity concern. That’s part of the reason why in our recent paper “Vulnerability Management: The Keystone of Cybersecurity Infrastructure”, so many organizations around the world expressed concern that they will be negatively impacted by a cyberattack in the near-term. That fact is that most midsized organizations don’t have dedicated information security professionals, much less a CISO.
Major security breaches are front page news and for many companies, that type of press can lead to customer churn, brand erosion, and decreasing cash flows, all of which have a negative impact on profits. Fear of being the next company making the headlines prompts organizations with and without CISOs to implement multilayered defenses. However, to achieve this, security tools must communicate with each other; discrete technologies that work in silos have proven to be less effective. Customers do not need more security products – they need more secure products.
Vulnerability Management (VM) platforms offer bidirectional integration with other technologies, and follow some of the essential principles that guide effective cyber security. As a first step, weaknesses in all software programs used by an organization are identified. Next, threats are prioritized based on common vulnerability and exposures (CVE) and a common vulnerability scoring system (CVSS) – this assessment is determined by the severity of the vulnerabilities and the risk appetite of each individual organization. Finally, vulnerability status and risk reports are communicated to all relevant parties and a recommended response is outlined.
Whereas Managed Security Service Providers (MSSPs) are too costly for most midsized enterprises, Managed Service Providers (MSPs) that already manage IT infrastructure for these resource constrained organizations can help. Over the past 2-3 years, leading MSPs have begun addressing the security needs of underserved midsized enterprise by offering a right-sized mix of proprietary and best-of-breed tools to create an integrated cyber defense platform. In the process, they are also helping organizations develop a suitable vulnerability detection and incident response process – not just suggested remediation steps. Importantly, MSPs typically offer a service-level agreement (SLA) that defines delivery windows for reporting incidents and initiating a response.
MSPs working with an organization provide more than just a service; they have to establish a strategic relationship with their customers based on trust. During an engagement, MSPs may have access to sensitive client information. As such, one measure of a top notch MSP is that the service provider has strong internal security processes and technologies to not only defend their own information, but also protect their privileged routes of access to customers’ networks.
To become a trusted and effective partner, MSPs must also handle issues relating to remediation without interrupting a customer’s business operations. They must adapt to customer needs and budget, understand the vertical in which they operate, and partner with leading cyber security vendors to provide effective protection, prevention, detection, and response solutions in a timely manner.
Digital Defense offers MSPs an intelligence-driven VM platform that provides organizational risk grading coupled with intuitive triaging. This enables MSPs to rank threats inside their own network as well as the networks of their customers. For MSP customers, Digital Defense’s platform enables their own resource-constrained teams to pinpoint issues that require prompt attention. Topological risk mapping enables security teams to understand which assets are on the network and the specific flaws that could place them at risk. The technology empowers MSPs and organizations’ IT teams to identify and address security challenges early by providing a clear and accurate picture of their security posture. This is made possible through Digital Defense’s contextual triaging and prioritization approach – an advanced capability in the vulnerability management market.
Digital Defense Frontline VM™ provides valuable integration with other security technologies to provide a holistic view of cyber security across an enterprise environment. Combined with its ease of use, Digital Defense is not only simplifying vulnerability management, but is actively working to alleviate the challenges facing resource constrained security teams.
Security challenges and complexities continue to increase, with sophisticated threats targeting a seemingly ever-growing exposure footprint. MSPs that are powered by a leading VM cybersecurity tool like Digital Defense are well positioned to be the strategic security partner of choice for midsized organizations that understand the need to stay one step ahead of cyber adversaries.
Related Resources
Need More In-Depth Info?
Contact us and one of our experts can help with any of our cybersecurity solutions.

