Fortra VM Datasheet
Scalable, Risk-based Vulnerability Management
With cyber attacks on the rise and a shrinking cyber security talent pool, IT teams are being asked to do more with less.
Fortunately, Fortra Vulnerability Manager (formerly Frontline VM™) is designed to streamline the identification and prioritization of system weaknesses, so you can maximize existing IT resources and mitigate risks swiftly and effectively.
Provided via our SaaS platform, Fortra VM is lightweight yet powerful and capable of scaling up or down to meet your changing business needs.
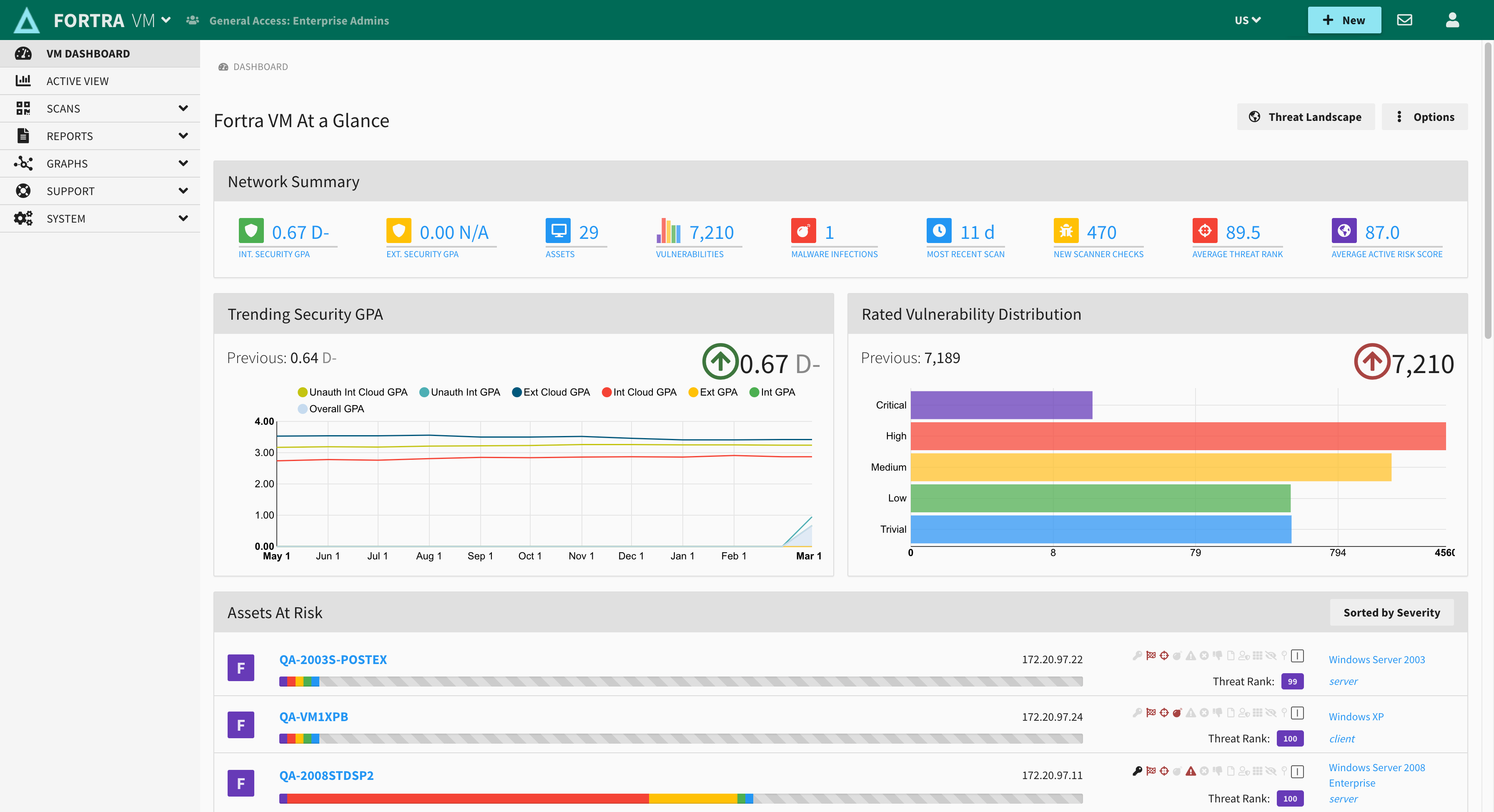
Fortra VM combines patented scanning technology with an easy to use GUI and asset data correlation to produce fast, accurate results (less than 1% false positives). The robust feature set of Fortra VM includes:
- Security GPA® security posture rating
- Insight peer comparison
- Network Map asset visualization
- Threat Rank exploitability context
- Connect API
Prioritize Security Threats for Faster Remediation
When vulnerabilities are detected, Fortra VM quickly provides prioritization and remediation information so immediate action can be taken.
Fortra's VM allows security teams to:
- Leverage Fortra's technical expertise and world-class customer support.
- Focus on core business functions to save time, money, and effort by reducing
the administrative burden and tedium of performing vulnerability scans with
complicated tools or unmanaged open source solutions. - Demonstrate your commitment to information security with comprehensive
reporting on the security posture of your network. - Detect possible security vulnerabilities and respond quickly with actions
based on your pre-defined security policies.
Some of our customers' favorite features:
Security GPA®
Security GPA is an easily understood metric that facilitates simpler security conversations. It is based on an algorithm that takes into account both the network security posture rating and the business risk associated with discovered vulnerabilities.
Client-defined Risk Ratings
Set the business risk level of your IP devices to a level based on the device’s criticality to the organization. Easily pinpoint areas of high risk and focus efforts on defending your enterprise.
Superior Customer Support
Fortra VM provides each account with a Client Advocate who personally understands the client's needs and provides superior customer support. Our loyal and happy user base consistently gives us 90+ customer satisfaction scores and Net Promoter Scores (NPS) of 75 or better.
Experience a powerful, user-friendly solution backed by top-shelf expert support.
Subscription Offerings for Organizations of Any Size in Every Industry
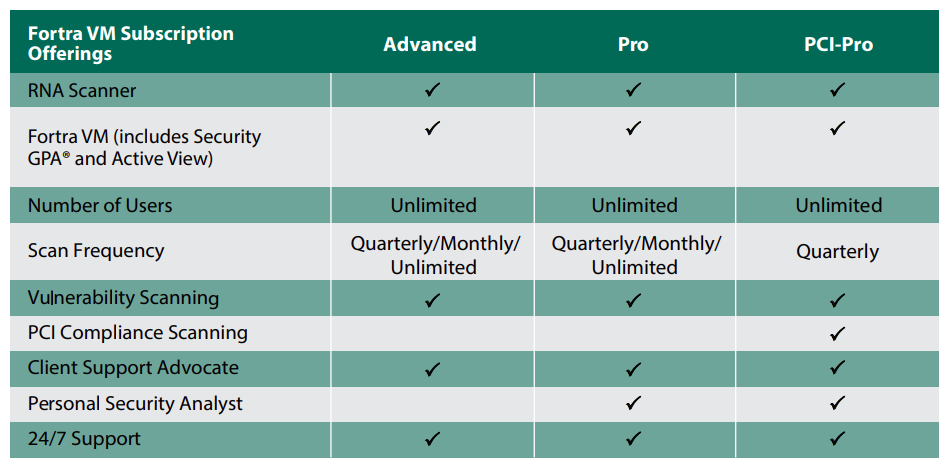
Vulnerability Management Advanced
Vulnerability Management Advanced is our flagship vulnerability management subscription offering. Powerful and effective, VM
Advanced is conveniently bundled into a rich, affordable, and easy to consume annual subscription that includes:
- VM scanning and features
- Unlimited users
- Client Advocate support
- Quarterly/monthly/unlimited scan frequency
- 24/7 support
- Access to Active View Dashboard
- User-friendly, aggregated scan results
- Robust filtering and labeling capabilities
- Patented host correlation
Vulnerability Management Pro
Vulnerability Management Pro provides the same industry leading solution subscription as VM Advanced, but adds a Personal Security Analyst (PSA). PSAs perform the work of running your scans, analyzing the results, generating reports, and providing direct remediation planning guidance for you, as opposed to your security team doing that themselves. It’s the ultimate outsource for all size organizations and is especially helpful for organizations that have limited security management time or expertise.
Ready to get Fortra VM?
Affordable, easy to use vulnerability management with excellent support.
Join the thousands of customers who trust Fortra VM to protect their business critical assets.
Copyright © Fortra, LLC and its group of companies. Fortra™, the Fortra™ logos, and other identified marks are proprietary trademarks of Fortra, LLC. | Privacy Policy | Cookie Policy | Sitemap

