Frontline Cyber Threat Risk Report Card™ Datsheet
Get advanced, real-time data collection with insight into the activity around your organization’s assests
Next Generation External Threat Alerts
Every day organizations are under attack. Many of them breached and unaware that their data has been compromised. According to industry reports, the average time to detect a breach is 256 days. During this time, adversarial individuals are in your network slowly extracting data
and using it to further breach your organization, employees or customers.
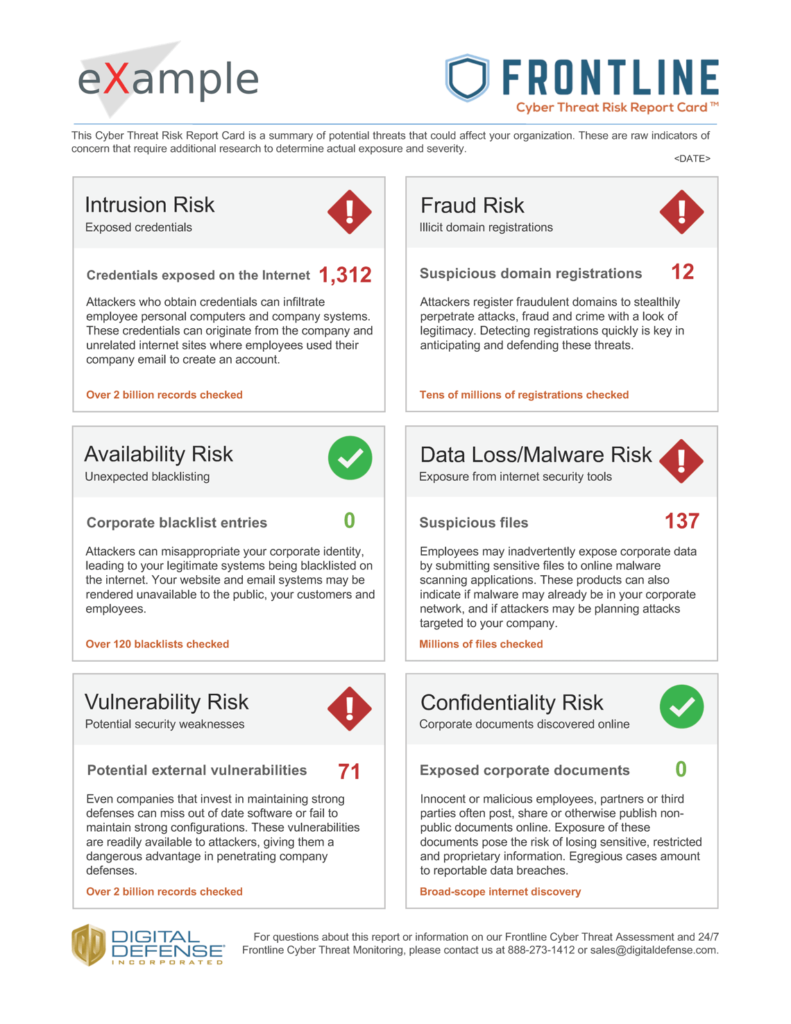
Data Collected and Reported
During Digital Defense’s research, we look at some critical points of exposure:
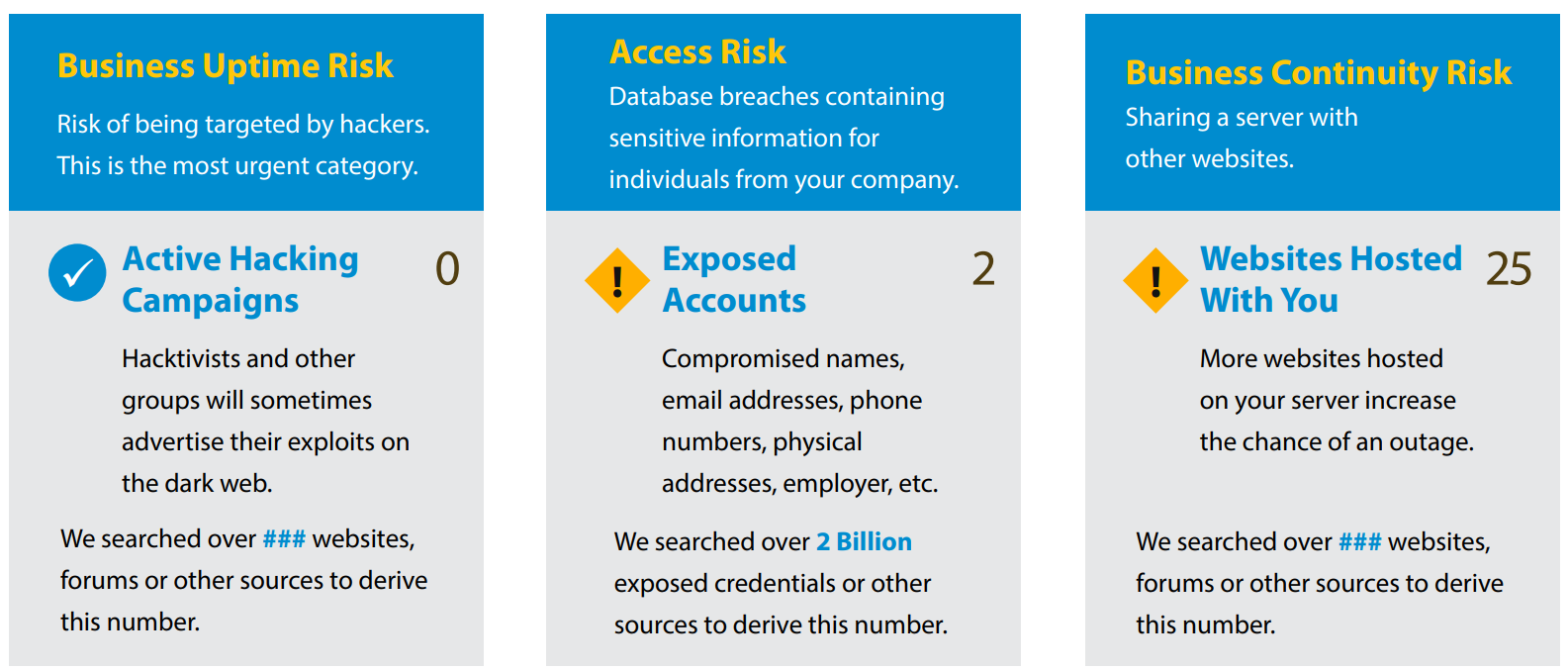
- Business Uptime - what is your overall risk of being targeted by hackers
- Access Risk - breaches of accounts or sensitive data
- Communication Risk - reputation of server and email practices
- Business Continuity Risk - hosted unidentified websites on your servers
- Theft & Fraud - website imitation vulnerability
- Publicly Exposed Servers - servers that may be easily accessed for hackers to steal information from
Evidence of Attacks
Technology Attack Surface
• Classless Inter-Domain Routing (CIDR)
• Public IP Space
• SSL Certificates
• Domain Names
Threat Vectors
• Adversary Groups
• Adversarial Online Sources for Monitoring
• Malicious Chatter
IP & Digital Assets
• Credentials
• Source Code
• Customers Lists
• Private Employee Information
Ready to get a Frontline Cyber Threat Risk Report Card™ Quote?
Easily Assess and Report Your Cybersecurity Weaknesses
Copyright © Fortra, LLC and its group of companies. Fortra™, the Fortra™ logos, and other identified marks are proprietary trademarks of Fortra, LLC. | Privacy Policy | Cookie Policy | Sitemap