
Reconnaissance Network Appliance (Frontline RNA™)
Overview
The Digital Defense, Inc. Reconnaissance Network Appliance (Frontline RNA™) is a preconfigured network based device used to perform network security assessments without requiring onsite staff.
Frontline RNA utilizes a proprietary Linux-based operating system to scan every IP accessible device (including servers, workstations, printers, IP phones, routers, switches, firewalls, etc.) on an organization’s network for vulnerabilities and weaknesses.
The assessment data is transferred through an encrypted network connection to the Digital Defense Secure Network Operations Center (SNOC). In conjunction with the Frontline.Cloud, the package provides an on-demand vulnerability management, network security assessment solution and network scanning tool that enables organizations to assess and manage business risk.
DDI NIRV™ Scanning Engine: Cross Context Scanning
At the heart of the RNA appliance is the NIRV scanning engine which represents a fundamental break from traditional network scanning methodology and allows the discovery of critical flaws often missed by other engines.
Whereas traditional network auditing technology focused on auditing services in isolation in a highly repeatable manner; the NIRV engine is capable of auditing networks as contiguous entities where information gleaned from each host, service, and application is reused throughout the network, allowing for a more thorough audit of its peers.
Select examples of this technology include:
- Webserver directory structure, scripts, and arguments discovered by webroot spidering or WSDL parsing on one service can be used to improve brute force, and fault injection on other hosts and services discovered; allowing tests to run multiple times in the same context if necessary for complete testing.
- Usernames, password hashes, and authentication tokens, gathered from RPC services are automatically tokenized, translated to different authentication formats and leveraged in an attempt to gain access to other services on both the host and network level.
- Critical SSL issues such as Heartbleed and BEAST are audited not just on traditional web-based SSL services but through the embedded SSL modes such as FTP, SMTP, POP3, VPN, RDP, RPC and even alternate-transport UDP based DTLS services.
- Weaknesses exposed in RMCP and IPMI embedded ARM baseboard interface auditing can be correlated and reused against the primary host operating system in order to expose networked side-channel access to otherwise secure systems.
By allowing the efficient tagging, tokenization, and re-use of data across all OSI layers, network services, and peer hosts on a network, NIRV better simulates the tactics a skilled attacker employs in modern data-breach attacks which often combine information gained through several moderate or low-level vulnerabilities to uncover more serious flaws and achieve a full system compromise.
The NIRV engine's cross context scanning technology has already been proven to be effective in real-world scenarios having resulted in dozens of critical CVE releases by major software companies. This includes the discovery of flaws in products which are among the most mature in the industry, having already undergone rigorous testing by traditional technology.
Digital Defense follows strict responsible disclosure policies when disclosing details of previously unknown flaws to software vendors, allowing vendors to respond and issue patches for any discovered issues and withholding any details that might benefit an attacker.
Key Benefits
- Effective full network scanning for comprehensive security risk reduction
- Extremely low false positive rate for efficient management of vulnerability remediation programs
- Automatic host reconciliation of previous scan results for unparalleled assessment quality
- Assignment of business risk weightings to hosts for sensible Security Grade Point Average (Security GPA®) assessment scoring
Installation & Maintenance
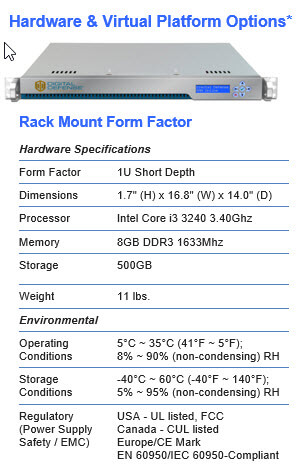
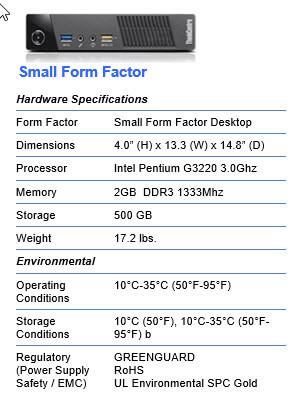
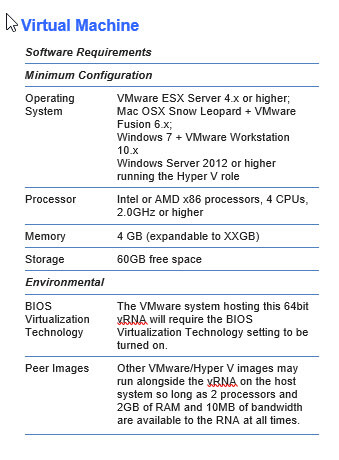
The number of RNAs required is dependent on the segmentation of an organization’s network; scan frequency, and number of hosts to be scanned. After placing one or more RNAs in optimal scanning location(s), the units require power and network connectivity.
Outbound network access on TCP port 443 or 22 (SSH) is required to keep the RNA properly maintained. RNA software updates are delivered to the RNA via this network connection automatically prior to the beginning of each vulnerability scan.
Latest Zero-Days
They're out there. We find them.
Most Recent Updates >>
Webinars & Events
Topics that will keep you up to date.
Learn With Us >>
Catch Our Latest Blog Posts
Thought provoking opinions that matter.
Read the Blog >>
Copyright © Fortra, LLC and its group of companies. Fortra™, the Fortra™ logos, and other identified marks are proprietary trademarks of Fortra, LLC. | Privacy Policy | Cookie Policy | Sitemap




